HP continues to shine a spotlight on print security with last years announcement of embedded print security features that aim to mitigate the threat of malware. So how vulnerable are printers to external attacks, and how can businesses limit their risks?
While the prevalence of connected printers and MFPs bring convenience and productivity, they also pose security risks. Along with the capabilities to capture, process, store and output information, most print devices also run embedded software. Information is therefore susceptible at a device, document and network level. Not only can confidential or sensitive data be accessed by unauthorised users – whether maliciously or accidentally – but network connectivity makes vulnerable print devices potential entry points to the corporate network.
Any data breach can be disastrous – leading to internal consequences such as the loss of IP or productivity, as well as external repercussions including brand and reputational damage, legal penalties and loss of customers.
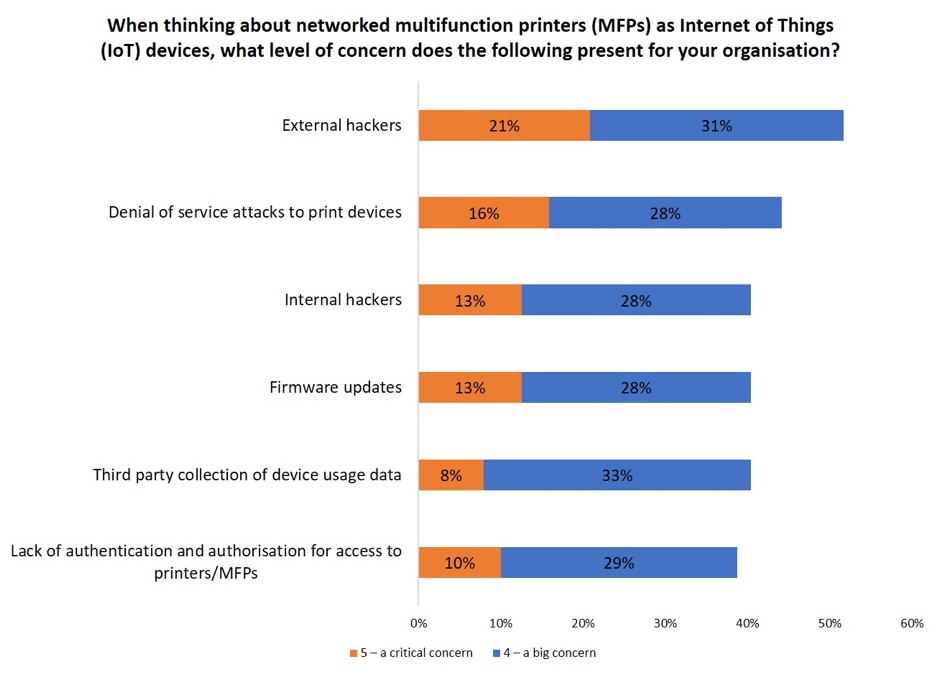
In today’s evolving Internet of Things (IoT) threat landscape, hackers that target printers with lax security can wreak havoc on a company’s network. Data stored on print devices can be used for fraud and identity theft and once hackers have a foothold, the unsecured print device provides an open door to the network. Compromised devices can be harnessed as botnets and used as launch pads for malware propagation, DDoS attacks and devastating ransomware attacks.
It is unsurprising to see that external hacking and DDoS attacks are top print security concerns amongst businesses. And although 95% of businesses indicate that print security was an important element of their overall information security strategy (55% say it was very important, and 40% fairly important) – just 25% reported that they are completely confident that their print infrastructure is protected from threats.
Mitigating the risk
To address these threats, print devices need to include robust security protection. Fortunately, more manufacturers are embedding security in new generation devices. HP’s enterprise printers for instance, can detect and self-heal from malware attacks through run-time intrusion detection and whitelisting. The newly announced HP Connection Inspector stops malware from “calling home” to malicious servers, stopping suspicious requests and automatically triggering a self-healing reboot. Meanwhile Xerox’s ConnectKey Technology enabled family of printers incorporates McAfee whitelisting technology which constantly monitors for malicious malware and automatically prevents it from running.
However, it only takes one rogue, unsecured device to weaken security. Whilst progress is being made on embedding security technology in the new generation of printers, the reality is that most organisations have a mixed fleet of devices – old and new, from different manufacturers.
Organisations should therefore undertake a print security threat assessment. Such assessments are commonly offered under a managed print/document service (MPS/MDS) contract, and seek to uncover security vulnerabilities.
Quocirca’s MDS study revealed that 31% of organisations have completed such an assessment with another 57% indicating that their assessment is underway. Organisations report that the top goal (65%) for a security assessment is to protect against new, advanced threats.
The most sophisticated security assessments such as that from MPP, not only make recommendations for device replacement and optimisation, but also offer ongoing and proactive monitoring of devices to identify potential malicious behaviour. Ultimately this requires that print devices are monitored as part of a broader security platform – MPP for instance, offers integration with security and information and event management (SIEM) tools.
The need for a multi-layered security approach
As both internal and external threats continue to evolve, a multi-layered approach to print security is essential to combat the security vulnerabilities that are inherent in today’s networked printers. Unless an organisation regularly tests its defences, it will be at risk of leaving a part of the print infrastructure exposed – enabling a skilled hacker to penetrate the network.
A business can be targeted no matter how big or small, so a comprehensive print security strategy that encompasses threat detection, preventative measures, threat monitoring and analytics alongside incident response and recovery is vital in today’s IoT era.
