Today we live in an enveloping world of technology where businesses can access numerous tools in assisting with the day to day operational functions and making of important decisions.
But, as technology becomes more advanced we create a brand-new set of problems. CYBER SECURITY – Data breaches, data theft, phishing, ransomware, and malware are perfect examples. Almost all of these vulnerabilities come from every-day usage of peripherals like printers, and businesses most definitely need to consider protecting the confidentiality of their documents.
The white-hat hacker known as Stackoverflowin hacked over 150,000 business and receipt print devices in 2017 to try and raise awareness around the importance of security on printing devices. Well known OEM’s such as HP, Canon, Epson and Brother were susceptible to the attack. Stackoverflowin advised that the script that he wrote “targets printing devices that have IPP (Internet Printing Protocol) ports, LPD (Line Printer Daemon Ports) and port 9100 exposed to external connections”. Devices that are Printers set up by default have zero security, the in-house network administrator would need to reconfigure the network to keep it secure.
SMB’s are prominent in the usage of MFP’s or multi-purpose printers, purely because of the ease of use in day to day operations. Features like faxing, scanning, photocopying and emailing have proven productive in cutting down time and costs. However, the problem with that is that it opens a multitude of security vulnerabilities.
Printer Hacking Security Breaches
How do the attacks take place? There are multiple ways hackers can perform malicious activities.
One of the most common attacks is when MFPs use an authentication mechanism that gives access to an employee via RFID, swipe-card, fingerprint, or manual entry of credentials (username and password). Hackers could evade the MFPs access to the network giving them the ability to print any documents and steal sensitive information.
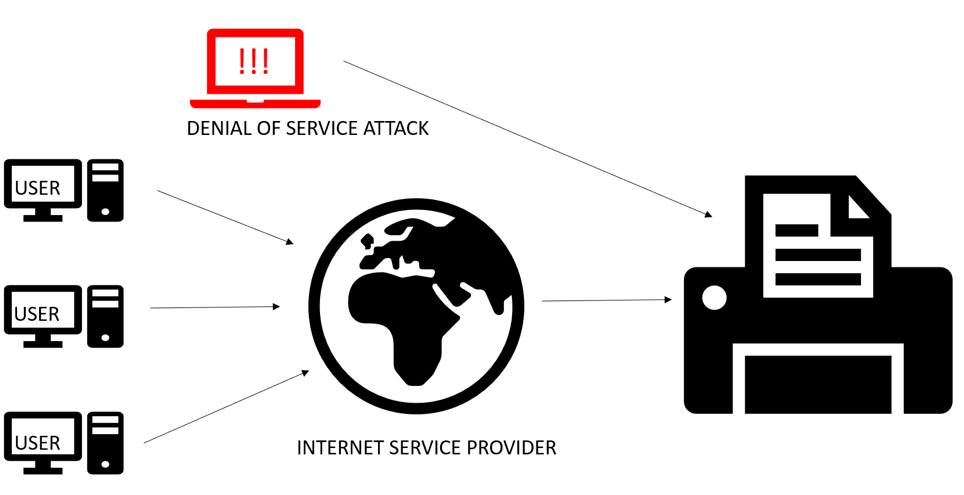
Another popular attack is a denial of service or DOS for short. This is when a printer is flooded with traffic from a botnet or an application that would render the printer useless, sometimes going as far as destroying it. Obtaining free or cheap software for conducting a DOS attack is not hard. Searching for results on Google or the “dark-web” is enough.
BYOD and printing has made businesses even more vulnerable to cyber attacks with many personal devices connected to a printer, or an array of printers. A hacker can inject your personal device with malware that can gain direct access to the corporate network, and thus its printers.
Security Measures for Printer Hacking
There are many security measures that your business can use to avoid attacks on printers. For example:
- Allow communications only with secured or trusted networks and hosts. The network administrator can easily configure which websites employees have access too. Get rid of unused protocols such as FTP, telnet and SNMP.
- Turning off unused protocols limits the way malware, viruses and worms can get inside the organisational network. Use a corporate-only network address for keeping the printer hidden from the internet.
Although hiding your businesses printers will certainly keep the attention away, it does not necessarily mean your printers are secured. If an inquisitive hacker manages to penetrate the network, he or she will be able to see the printer. If there are no security measures on the printers, then it will be easy for a hacker to intercept documents, steal sensitive information or sabotage its operations.
As digital grows to solve every-day business tasks in the lives of millions, so does the need of cyber-security.
It is increasingly becoming easier to breach devices and steal sensitive information. In today’s global space, businesses have an obligation to deploy printer related security measures.
